
WordPress https
Google recently announced that it has started using HTTPS as a ranking signal. So to improve your SEO results you can choose to ONLY use HTTPS for your WordPress site. For this to work you have to have a valid certificate in place (obviously).
Setting up a “SSL only” blog takes two steps.
1. Update your .htaccess file
Go to your WordPress installation folder and edit the .htaccess file in there. Below the line
RewriteEngineOn
add the following two lines:
RewriteCond %{HTTPS} !=on
RewriteRule ^/?(.*) https://%{SERVER_NAME}/$1 [R,L]
The two rules above will take care for the redirection (in case the user visited your http site) to the https site.
2. Update the WordPress blog settings
Go to the dashboard of your WordPress site and navigate to Settings -> General . Change the WordPress Address and Site Address to use the htpps URL:
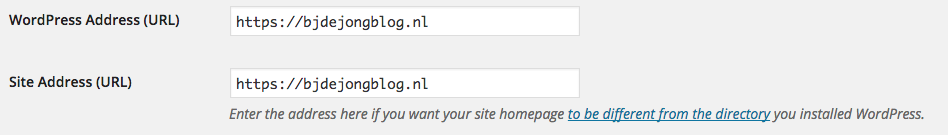
WordPress https
Ok that is all. Your visitors will now always be redirected to the https version of your website.


