Use the ProFTPD TLS protocol
 In this post I will describe how to configure the ProFTPD server to use the TLS protocol. Out of the box the ProFTPD configuration uses plain FTP on a Virtualmin installation; this is not secure. Configure your ProFTPD server to use the ProFTPD TLS protocol for better security.
In this post I will describe how to configure the ProFTPD server to use the TLS protocol. Out of the box the ProFTPD configuration uses plain FTP on a Virtualmin installation; this is not secure. Configure your ProFTPD server to use the ProFTPD TLS protocol for better security.
To configure ProFTDP to use the TLS protocol for communication follow the steps below.
Log in to your Virtualmin admin site and goto Servers -> ProFTPD server . Select Edit config files (be sure that the file /etc/proftpd/proftpd.conf is selected). Make the following changes to the file.
- Change the setting PassivePorts to 65000 65500 (these ports wil be opened in your firewall later on).
- Go to the section with the header This is used for FTPS connections and uncomment the include statement for /etc/proftpd/tls.conf .
Save this configuration files and select “Edit config files” again (now the new included file will appear in the dropdown list “Edit directives in file”). Select the file “/etc/proftpd/tls.conf” and press the Edit button.
In the file “/etc/proftpd/tls.conf” add the lines below immediately after the “<IfModule mod_tls.c>”. Adding these lines will enforce TLS connections:
TLSEngine on TLSRequired on TLSRSACertificateFile /home/username/proftpd.pem TLSRSACertificateKeyFile /home/username/proftpd.pem TLSCipherSuite ALL :!ADH:!DES TLSOptions NoCertRequest TLSVerifyClient off TLSRenegotiate ctrl 3600 data 512000 required off timeout 300 TLSLog /var/log/proftpd/tls.log
To prevent users from leaving there home directory when browsing with the FTP client you have to change the setting “Limit users to” Directory “Home directory”. In VirtualMin goto “Servers -> ProFTPD Server -> Files and Directories”.
Next step is to generate a certificate file for our TLS connection. As you can see above in the TLS configuration this file has to be stored at /home/username (you could ofcourse choose a different location…).
Lets create a certificate for the TLS connection at the appropriate location; give the new certificate file restricted permissions:
cd /home/username openssl req -x509 -nodes -days 365 -newkey rsa:1024 -keyout proftpd.pem -out proftpd.pem chmod 600 proftpd.pem
Now restart your ProFTPD server. Either via the Virtualmin interface or with:
service proftpd restart
The ProFTPD server is up and running now but it is not yet accessible because you have to open the firewall ports specified on the PassivePorts setting. Execute the commands below on your server (assuming you are going to TLS over port 21 and passive ports are in the range 65000 – 65500):
sudo iptables -A INPUT -p tcp --dport 21 -j ACCEPT sudo iptables -A INPUT -p tcp --dport 65000:65100 -j ACCEPT sudo iptables -A PREROUTING -t nat -p tcp --dport 65000:65500 -i eth0 -j DNAT --to xxx.xxx.xxx.xxx
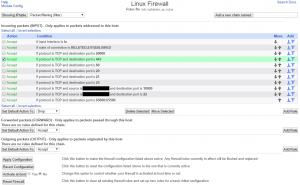
After this your firewall settings should something like this:
Now to test this setup install FileZilla (or any other FTP client like WinSCP) and create a new connection; follow the steps below
Download the FileZilla FTP client and start the FTP client; create a new site as described below.
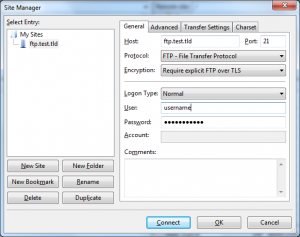 Type Ctrl+S (Site Manager)
Type Ctrl+S (Site Manager)
Press the New Site button
Host: the name of your FTP host (domain name in most cases)
Port: 21
Protocol: FTP – File Transfer Protocol
Encryption: Require explicit FTP over TLS
Logon type: Normal
User: your username
Password: your password
On the “Transfer settings” tab select “Passive” for the transfer mode.
When you click connect a warning will appear about a unknown certificate (if not your configuration is not correct and you have to double check your settings). The warning looks something like this:
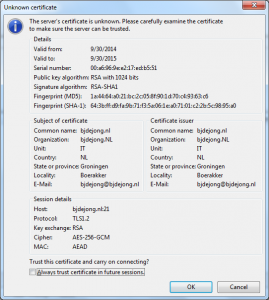
Select Ok and now you should see the FileZilla file browser; on the left your local files and on the right your remote files.